
We continue to talk about privacy and let's see how Xiaomi seems not to be very thick on the piece. Some time ago we faced the thorny question of the data used (or not) by the brand and how, for example in India, the problem was solved with a new version of MIUI. Which by the way comes out today. But here we will see an error, a flaw, discovered by a member of XDA on Reddit regarding the Xiaomi MI 9T fingerprint ID sensor: this would turn the sensor itself into one camera endangering some sensitive data.
A flaw discovered in Xiaomi's fingerprint sensor: a particular device would have allowed, via an app, to record through it
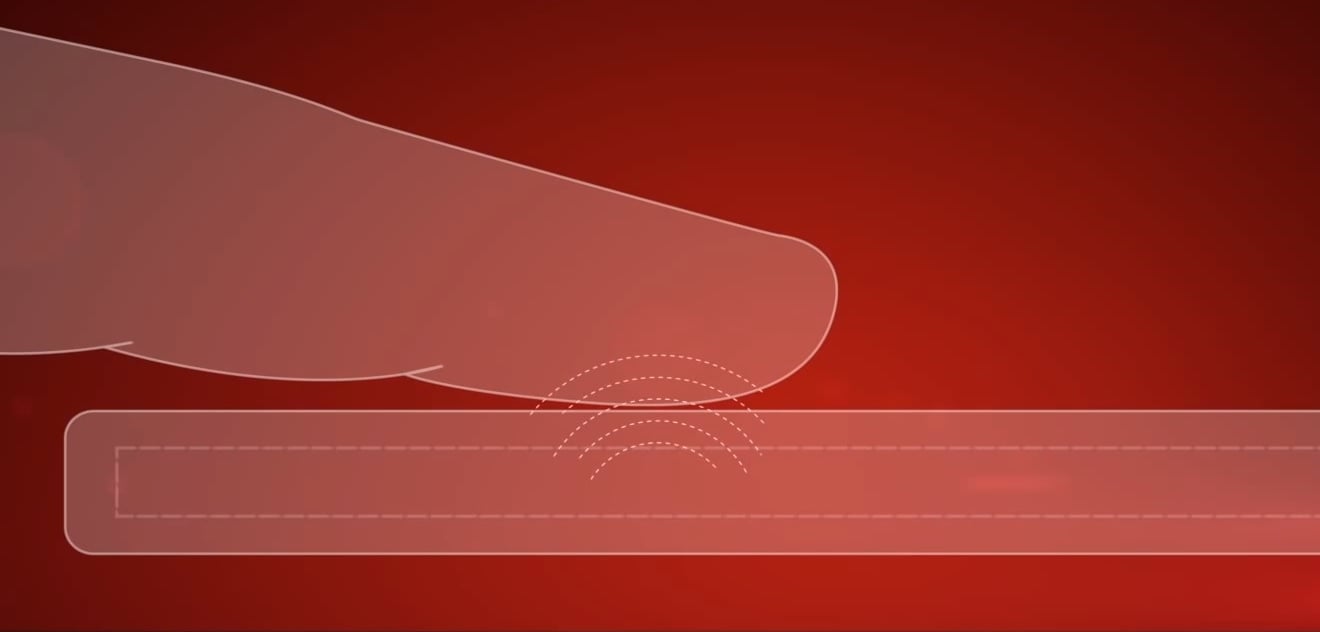
In a Twitter post, theXDA Developers Editor-in-Chief has made users aware of an important one security flaw. It has in fact reported the testimony of a user published on Reddit. Would you ever have said that a fingerprint sensor could turn into a camera? Do not worry, the resolution of this sensor is minimal and however dangerous the flaw is it does not allow you to see well through the lens. Let's see the question though, because despite the poor image quality, they were big doubts raised.
A Redditor found a hidden activity on a Xiaomi phone that lets you see the raw feed from Goodix's optical under-display fingerprint scanner.https://t.co/RKpjDTdgzG
OEMs really shouldn't be leaving these debug apps in production builds… pic.twitter.com/fnEpvPZtol
- Mishaal Rahman (@MishaalRahman) August 10
In short, a user would have found a hidden activity on his I 9T , see the feed using the sensor below the display which is used to unlock the device. In short, as we anticipated, that is used sensor like a camera. With the app Activity Launcher, this user was unable to find seemingly hidden activities to the rest of the users. However, this does not mean that the problem does not exist, on the contrary: any attacker could download the application on our smartphone and record important data.
As mentioned earlier, the quality of the sensor that captures the image of the fingertip is very poor: it would be difficult even for an expert to record sensitive data. But the problem is upstream: biometridal data should be protected by Trusted Execution Environment, a super secure area of the smartphone. The certification of this protection is mandatory (at least in Europe) and if a device does not pass it, it cannot be certified and placed on the market. So the question we ask ourselves is: why is there such a security flaw? Have adequate checks not been made?
Through | Android Authority, Twitter

![Xiaomi Redmi 9 - Smartphone 3GB 32GB, 6.53" FHD+ Display, AI Quad Camera 13 MP, 5020 mAh Battery, Purple [Spanish Version]](https://m.media-amazon.com/images/I/41VaITUBRaL._SL500_.jpg)







